NO-STEALER ENGINE
A comprehensive PowerShell scanning engine for detecting stealer-type malware on Windows. Chains hash, static, memory, C2, and behavioral analysis into a single tool.
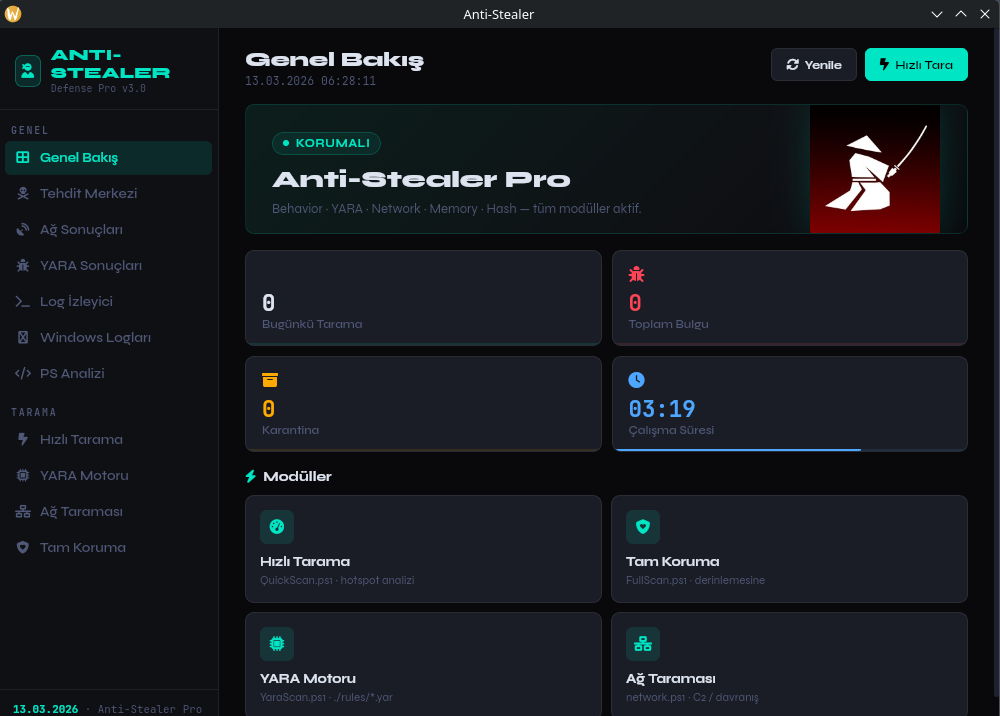
A comprehensive PowerShell scanning engine for detecting stealer-type malware on Windows. Chains hash, static, memory, C2, and behavioral analysis into a single tool.
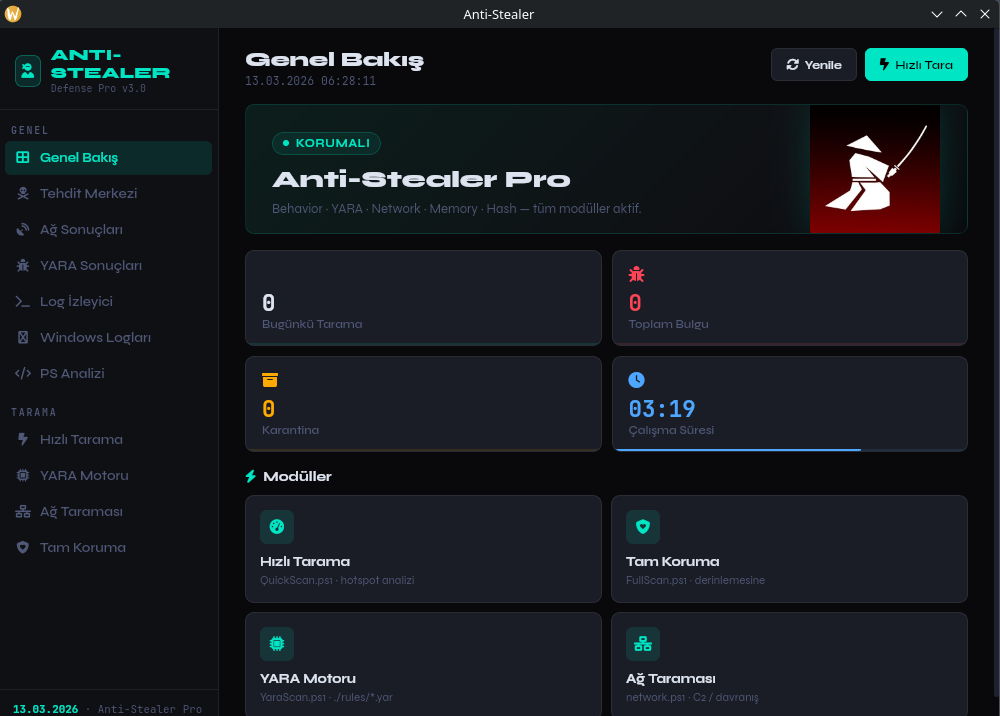
Modules run sequentially, chaining static, memory, and behavioral analysis to catch what single-layer tools miss.
SHA256 exact match against a maintained database of known stealer binaries. Fastest path to a Confirmed verdict.
SHA256Extracts printable strings and scores similarity against signature sets. Catches polymorphic variants where hashes change but string patterns don't. Thresholds: 0.01 → Low / 0.08 → Potential.
JACCARD > 0.08Reads live process memory regions and matches against in-memory signatures. Detects injected payloads that never touch disk.
LIVE PROCESSCompares active TCP connections to a curated C2 IP/domain database. Returns Confirmed-C2 on a match — use results to generate firewall rules.
TCP · LIVERule-based checks: suspicious TLDs, non-standard ports, multiple simultaneous domains, and known-bad process names in outbound connections.
RULE-BASEDWeighted Jaccard similarity across API calls, registry writes, file operations, and command-line patterns using NO-ST JSON rules. Threshold ≥ 0.30 triggers a finding; ≥ 0.60 is High risk.
NO-ST RULESRequires PowerShell 7+ and Windows 10/11 (64-bit). Run as Administrator for full system access.
Download install.ps1 and kural.txt from the repository and place them in the same folder.
Right-click PowerShell 7 → Run as Administrator. Then bypass execution policy for the session.
ADMIN REQUIREDExecute both scripts in order from your folder. If you hit a Python build error, install C++ Build Tools from the Microsoft link, restart PowerShell, then run again.
PS7 REQUIREDInstall pywebview via pip, then run UI.ps1 in PowerShell 7 (Admin) for the graphical interface.
Anti-Stealer is research-oriented — it generates shareable rules and structured telemetry, not just a pass/fail result.
Reverse-engineer stealer families, write and validate YARA/Sigma rules against a real multi-layer behavioral engine.
Use NO-ST JSON rule output for signature generation, test automation, and AV vendor submissions.
Rapid on-host scanning, structured telemetry, and prioritized risk levels for fast incident triage.
Expand C2 and SHA databases, export structured IoC data to open intelligence platforms.
Every scan produces structured, shareable artefacts — not just a clean/infected verdict.
Static string and byte-pattern rules ready for AV vendor submission or VirusTotal upload.
Normalized behavioral patterns compatible with SIEM platforms and log-based detection pipelines.
Structured API calls, registry, file, and network telemetry powering the behavioral detection module.
One JSON object per finding: module, risk level, family classification, PID, and similarity score.

Add signatures, tune Jaccard thresholds, or submit a PR with a new stealer family. The community makes the rules sharper.